
Table of Contents
Microsoft’s Cross-tenant features
When it comes to the cross-tenant access features, Microsoft has a strong road plan so far. There won’t be any more external users or jumping between Teams tenants when you require access to various tenants, which we all know you do.
In January this year I wrote on the different features and at that time Cross-tenant sync was in Public Preview but not anymore.
See my previous blog here.
Cross-tenant synchorinization
Azure AD companies can employ External Identities cross-tenant access settings. You have fine-grained control over how external Azure AD organizations interact with you (inbound access) and how your users interact with external Azure AD organizations thanks to cross-tenant access settings (outbound access).

Cross-tenant User Data Migration
Microsoft released Cross-tenant user data migration last year. As an overview, you can migrate from tenant to tenant users mailboxes and OneDrive content.
You can read more on my previous blog concerning this feature.

So, cross-tenant has been a hot topic for a while now and now it’s time for next feature to the cross-tenant family.
What is Cross-tenant synchronization?
Creating, updating, and deleting Azure AD B2B collaboration users across tenants in an organization is automated through cross-tenant synchronization. Users may access applications and work together across tenants, and the organization can still develop thanks to it.
The following objectives of cross-tenant synchronization are crucial:
- Collaboration that is seamless for a multi-tenant business
- Automate B2B collaboration user lifecycle management in a multi-tenant company.
- Delete B2B accounts instantly if a user leaves an organization.
Who should use it?
Organizations have different needs from different reasons. Currently Microsoft advises only clients with the following to use this feature
- Organizations that own multiple Azure AD tenants and want to streamline intra-organization cross-tenant application access.
- Cross-tenant synchronization is not currently suitable for use across organizational boundaries.
What doesn’t work?
- Cross-tenant sync doesn’t improve the present Microsoft 365 or Teams experiences. Users who are synchronized will use the same cross-tenant Teams and Microsoft 365 experiences as any other user of B2B collaboration.
- Does not synchronize contacts, groups, or devices.
What you need for it?
- A source and target Azure AD tenant with a Premium P1 or P2 license
- An account in the source tenant with the Hybrid Identity Administrator role to configure cross-tenant provisioning
- In the target tenant Security Administrator role to configure cross-tenant access settings.
What topologies are supported?
Cross-tenant synchronization can provide a flexible solution for collaboration by allowing users to share data and access resources across different tenants. However, it’s important to note that every organization has unique requirements and needs, and the configuration of cross-tenant synchronization should be tailored to fit those needs. Each cross-tenant synchronization configuration is one-way, meaning that it only synchronizes data in one direction between two Azure AD tenants. This allows for different topologies to be configured, such as:
- Synchronizing users from one tenant to another
- Synchronizing groups and group membership
- Synchronizing resources such as calendars and contacts
- Synchronizing attributes such as name, email address, and phone number
However, it’s important to keep in mind that cross-tenant synchronization can be a complex process and that it can have security, compliance and management implications. It’s important to be familiar with the tenants and the data, and to have a good understanding of the security and privacy requirements, before setting up cross-tenant synchronization.
Attributes of the feature:
- Based on the Azure AD provisioning engine.
- Is a push process from the source tenant, not a pull process from the target tenant.
- Supports pushing only internal members from the source tenant. It doesn’t support syncing external users from the source tenant.
- Users in scope for synchronization are configured in the source tenant.
- Attribute mapping is configured in the source tenant.
- Extension attributes are supported.
- Target tenant administrators can stop a synchronization at any time.
More on Learn,

User synchronization
When an application uses automatic user provisioning, Azure AD automatically creates and updates user accounts in the app based on criteria like user and group assignment at predetermined intervals, usually every 40 minutes and this time is what Cross-tenant synchronization uses and it can’t be currently changed.
See more on App based provisioning

How to setup?
Target tenant setup
You will find the solution from https://entra.microsoft.com/#view/Microsoft_AAD_Connect_Provisioning/CrossTenantSynchronizationMainMenuBlade/~/Configurations/menuId/CrossTenantSynchronizationMainMenuBladeId
From there you can create a configuration (App registration)

Give it a descriptive name. I will add App in the name and soon you will see why

And you will see the created configuration

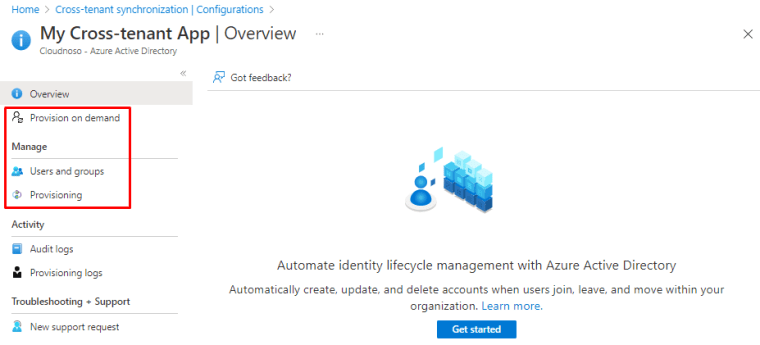
Once you open the configuration, you will see the following configurable options under it
Under provisioning you can change from Manual to Automatic but during Preview you cannot change it back. I will keep it manual for now.

Let’s jump to Entra and I will show you why I named it as application. Open App registrations under Entra and you will see an familiar App registration.

And we can see it also under Enterprise applications, just wanted to share this so you understand what we are dealing with

Again jumping back to Azure portal and now under https://portal.azure.com/#view/Microsoft_AAD_IAM/CompanyRelationshipsMenuBlade/~/CrossTenantAccessSettings

Choose “Allow users sync into this tenant” to allow sync

And under the organizational config open Trust settings

Suppress consent setting must be checked in both the source tenant (outbound) and target tenant (inbound)

Source tenant setup
Add users that you want to sync to App registration as users, either in the configuration or under Enterprise applications

In the source add cross-tenant sync application and switch mode to Automatic

And the copy Tenant ID of the target tenant, you can do this with Entra, Azure portal or with the following page
Then click on “Test connection” and you will be presented with an error or success, my case success!

Once test is done, hit save and you will see more menus under the application. For mapping (that you can edit) and for notification email and threshold for deletion

Mappings

You can remove mapping or add new ones

You can add a new mapping if needed.

See more from Microsoft on the mapping and how it works

And you have advanced options like request additional attributes, use expression builder and review your schema as JSON.

Schema export allows you to edit or download your schema

Provisioning
You can test out the provisioning from Provision on demand with 5 selected users at the time

Once you select the users and run demand provisioning, you will see the following error if the user isn’t attached to the app registration

Once the user is added, you can see them inside the provisioning page

And the will be provisioned, you can see the details at attribute level and the data flow on what attributes have been provisioned

Once you are done, switch that sync to On to schedule it every 40 mins.

And start the initial sync

Provisioning logs
Once the user is provisioned, you will the status of the different parts inside the status page and the provisioning logs are one the left side

When you open the logs, you will see skipped and successful syncs

Application owners can view logs for their own applications. The following roles are required to view provisioning logs:
- Reports Reader
- Security Reader
- Security Operator
- Security Administrator
- Application Administrator
- Cloud Application Administrator
- Global Administrator
- Users in a custom role with the provisioningLogs permission
Limitations and know issues
Microsoft has an extensive list of what working and what not, see it from Learn. Again, if you have any feedback, reach out to them or us MVPs to make the product better.

Tenant restrictions v2 (Preview)
One more things that I would like to mentioned is Tenant restrictions that has reached version 2 in it’s timeline. Features are evolving all the time and based on the feedback they will keep doing it.
With Tenant restrictions you may restrict what your users can access when they sign in from your networks or devices using an external account to boost security.
You may restrict which external apps users of your Windows devices can access when they log in with different accounts by using the Tenant restrictions settings, which are part of the cross-tenant access settings.

Closure
Cross-tenant story keep expanding and these are really useful features in the world of acquisitions and mergers.
Try it out for our self and give feedback to Microsoft if something isn’t right just shout it out in social. These things are developed for us all to have easier life as Cloud professionals.
Have a good one!


 RSS - Posts
RSS - Posts